Nick Apseloff
My name is Nick Apseloff, (pronounced /ˈæpsəlˌɒff/; 22 August 1992 - present) and I am currently a student in Mr. Bui's advanced topics class.
Contents
Goals
1st Quarter
1. Set up a small network of 3 computers using a hub. [X]
2. Use a packet sniffer to capture messages sent from one computer to another on the network. [X]
3. Research network security and vulnerabilities and document findings. [ ]
Documentation
1st Quarter
Goal 1
Willie Stehm, AJ McLennan, and I set up a network of three computers. We installed Xubuntu 8.04 (a Linux distribution) on each machine and then networked them together using ethernet cables (like the own shown at the top of the page) and a hub. We chose Xubuntu as our operating system because it is completely free to download and use and requires much less memory to operate (which was a necessity since all three computers are relatively old[1] ).
Goal 2
We initially tried to get the program 'talk' working on the machines so we could easily send messages between two of the computers in an attempt to view the packets transmitted on the third computer. After a few days of trying to get it to work, with no success, we settled on using Pidgin (a messenger client that is compatible with AOL Instant Messenger).
We then downloaded a packet sniffer called 'Wireshark' and ran it on one of the computers. On AJ's computer, he signed onto AOL Instant Messenger using his own screen name. By changing the display filter of the packet sniffer to only show AIM packets, we were able to see his screen name when he logged on. It was difficult to decipher which packets corresponded to what he was doing, but after getting familiar with the descriptions of the packets it was easy to pick out the ones that were messages. We were able to read outgoing and incoming messages as well as buddy info that the other computer was viewing.
On Willie's computer, I typed in a random password to sign on just so I could see if we could view the password sent to AOL. We found the outgoing packet and not surprisingly, the password was not sent in plain text; it was sent as a password hash using the MD5 algorithm, short for Message-Digest algorithm 5. This algorithm uses a one way hash function (one way meaning that the function cannot be reversed) that translates the password to a 128-bit hash value (32 characters consisting of 0-9 and a-f). The purpose of the password hash is to prevent exactly what we were trying to do. We successfully sniffed the packet that contained the password sent, but all we got was the following irreversible password hash: 51e3ed91700bee528a11e333ab25e6d2. In Layman's terms, when you type in a password to sign into something, the password gets jumbled up into random letters and numbers before being sent, so anyone trying to steal your password by sniffing your packets will not be able to, or at least have a very difficult time doing so. It is theoretically possible to recover a plain text password from an MD5 password hash using a rainbow table, but this is not an easy process by any means.
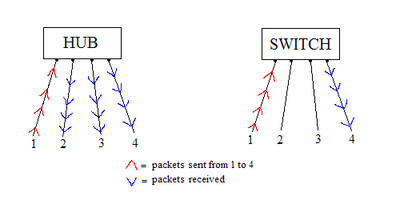
The reason that this packet sniffing worked was because we were using a hub, rather than a switch, to connect our computers in the network. Hubs broadcast the packets sent by one computer to all ports, so viewing the packet activity of another computer is quite simple (see Figure A). On the other hand, switches send the packets to only the desired port, so others on the network cannot listen in on your traffic. Switches have replaced hubs almost entirely because of this blatant security flaw, but hubs are still used in some situations such as where security is not a necessity.