Difference between revisions of "Nick Apseloff"
| Line 1: | Line 1: | ||
<!--DO NOT EDIT MY PAGE--> | <!--DO NOT EDIT MY PAGE--> | ||
[[Image:Cat_5.jpg|border|200px|right]] | [[Image:Cat_5.jpg|border|200px|right]] | ||
| − | |||
| − | |||
My name is <b>Nick Apseloff</b>, (pronounced /ˈæpsəlˌɒff/) and this is my wiki for [http://www.paulbui.net/ Mr. Bui's] advanced topics class. | My name is <b>Nick Apseloff</b>, (pronounced /ˈæpsəlˌɒff/) and this is my wiki for [http://www.paulbui.net/ Mr. Bui's] advanced topics class. | ||
Revision as of 18:59, 6 October 2008
My name is Nick Apseloff, (pronounced /ˈæpsəlˌɒff/) and this is my wiki for Mr. Bui's advanced topics class.
Contents
Goals
1st Quarter
1. Set up a small network of 3 computers using a hub. [X]
2. Use a packet sniffer to capture messages sent from one computer to another on the network. [X]
3. Attempt to read an e-mail sent through the hub from another computer using the same packet sniffer from goal #2. [ ]
Documentation
1st Quarter
Goal 1
Willie Stehm, AJ McLennan, and I set up a network of three computers. We installed Xubuntu 8.04 (a Linux distribution) on each machine and then networked them together using ethernet cables (like the own shown at the top of the page) and a hub. We chose Xubuntu as our operating system because it is completely free to download and use and requires much less memory to operate (which was a necessity since all three computers are relatively old)[1].
Goal 2
We initially tried to get the program 'talk' working on the machines so we could easily send messages between two of the computers in an attempt to view the packets transmitted on the third computer. After a few days of trying to get it to work, with no success, we settled on using Pidgin (a messenger client that is compatible with AOL Instant Messenger).
We then downloaded a packet sniffer called 'Wireshark' and ran it on one of the computers. On AJ's computer, he signed onto AOL Instant Messenger using his own screen name. By changing the display filter of the packet sniffer to only show AIM packets, we were able to see his screen name when he logged on. It was difficult to decipher which packets corresponded to what he was doing, but after getting familiar with the descriptions of the packets it was easy to pick out the ones that were messages. We were able to read outgoing and incoming messages as well as buddy info that the other computer was viewing.
On Willie's computer, I typed in a random password to sign on just so I could see if we could view the password sent to AOL. We found the outgoing packet and not surprisingly, the password was not sent in plain text; it was sent as a password hash using the MD5 algorithm, short for Message-Digest algorithm 5. This algorithm uses a one way hash function (one way meaning that the function cannot be reversed) that translates the password to a 128-bit hash value (32 characters consisting of 0-9 and a-f). The purpose of the password hash is to prevent exactly what we were trying to do. We successfully sniffed the packet that contained the password sent, but all we got was the following irreversible password hash: 51e3ed91700bee528a11e333ab25e6d2. In Layman's terms, when you type in a password to sign into something, the password gets jumbled up into random letters and numbers before being sent, so anyone trying to steal your password by sniffing your packets will not be able to, or at least have a very difficult time doing so. It is theoretically possible to recover a plain text password from an MD5 password hash using a rainbow table, in which the hash value is compared to an extensive list of known hash values and their plain text form, but this is not a very feasible tactic. A seven character password has 6.98 x 10^13 possible combinations, and having a hash list of every single one of them would require hundreds of terabytes of storage.[2]
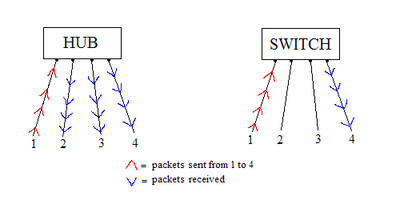
The reason that this packet sniffing worked was because we were using a hub, rather than a switch, to connect our computers in the network. Hubs broadcast the packets sent by one computer to all ports, so viewing the packet activity of another computer is quite simple (see Figure A). On the other hand, switches send the packets to only the desired port, so others on the network cannot listen in on your traffic. Switches have replaced hubs almost entirely because of this blatant security flaw, but hubs are still used in some situations such as where security is not a necessity.
Goal 3
After our success with sniffing instant messenger packets, we decided the next step would be to try to do the same with e-mail. On Willie's computer we had Wireshark running and sniffing packets with a display filter only showing HTTP packets. We were unable to locate the packet that contained the message when AJ sent an e-mail from his computer, but it was surprisingly easy to intercept his Gmail chat conversation.
We started by looking at all of the packets that had the word 'mail' in the description header. The packets that had the word 'POST' in the description were Gmail chat packets, and we began to look through the detailed packet information. We found AJ's e-mail address, the e-mail address of the person AJ was chatting with, and even the text AJ was sending to that person. Another interesting thing we discovered was that every time AJ moved his mouse, a packet would be sent with the text "mouse_move" in the details. We deduced that this packet is what determined whether his computer was idle or not, and after a certain amount of time of him not typing and not moving his mouse, Gmail chat would automatically set his status as 'idle'.
In addition to seeing his chat activity, we were able to read messages from his inbox. Gmail refreshes the inbox after a certain period of time, and doing so resulted in an incoming packet that contained all of his inbox messages in plain text form. We were able to read the address of who the e-mail was from, as well as the subject and body of the e-mail.
I had previously assumed that the Gmail chat would be encrypted, but after further research I figured out why we were able to read AJ's messages. When communicating over Google Talk using the downloaded program, similar to AOL Instant Messenger, the connection is encrypted, but when using chat over HTTP in Gmail, there is no encryption.[3] This is a serious security flaw that obviously can be exploited with ease. I never would have known that there was no encryption had I not been experimenting with it. Essentially, sending information over a non-encrypted connection is like sending information to someone in a postcard; anyone who sees the postcard can read what is written on it because there is no form of security.